Creating your recommendation
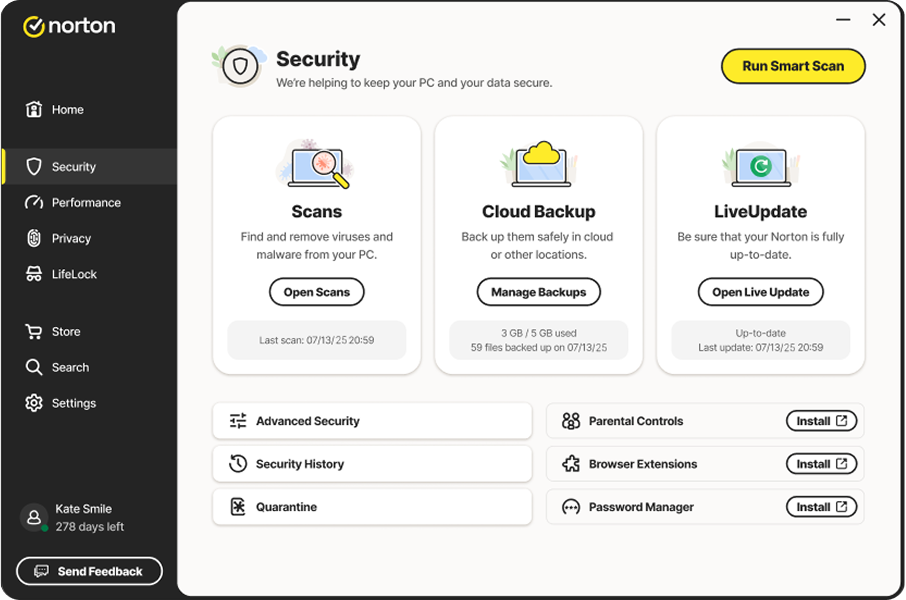
Norton technology blocks millions of cyberthreats every day.
Trusted by millions of customers around the globe.
Your personalized matches
*Important subscription, pricing, and offer details:
- By subscribing, you are purchasing a recurring subscription which will automatically renew.
- The price quoted today is valid for the offered introductory term. After that, your subscription will be billed at the applicable monthly or annual renewal price here. The price is subject to change, but we will always send you a notification email in advance.
2 Requires an automatically renewing subscription for a product containing antivirus features. For further terms and conditions, please see norton.com/virus-protection-promise.
4 Only available on Windows systems (but not in S mode or on ARM processors).
21 Utilities Ultimate, Driver Updater, Software Updater, and Cloud Backup features are only available on Windows (excluding Windows in S mode and Windows running on ARM processor).
22 Private Browser is only available on Windows (excluding Windows in S mode and Windows running on ARM processor) and Mac.
‡ Monitoring available on Windows™ PC, iOS, and Android™ devices. Not all features available on all platforms.
§ Monitoring not available in all countries and varies based on region.
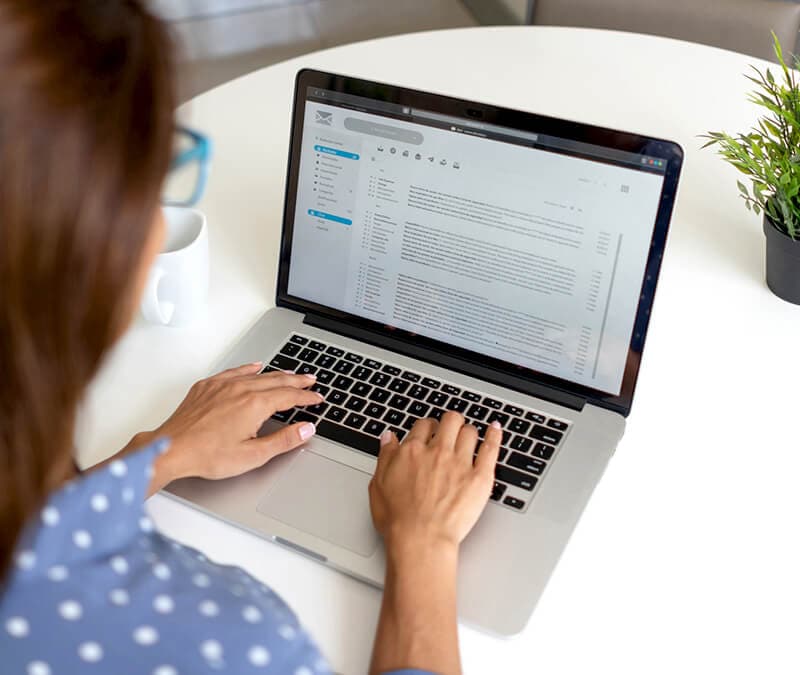
Scams
Learn about the latest online scams and get tips to stay protected.
Free Tools & Trials
Powerful protection, free to try. Browse free tools and test-drive Norton products.
Try Norton 360 Deluxe free*
Harness the power of AI for robust protection against malware, scams, and other digital threats.
*Terms apply
Other Topics
Explore more topics in digital security.



































Want more?
Follow us for all the latest news, tips, and updates.