What is Pegasus spyware, and how to detect and remove it
Pegasus spyware is a sophisticated surveillance tool known for targeting national security threats — as well as journalists and activists. It’s typically not a threat to the average person, but it isn’t the only type of spyware out there. Learn how Pegasus works, then get Norton 360 to help defend against other, more common forms of spyware.

- What is Pegasus spyware?
- How does Pegasus spyware work?
- Known Pegasus spyware attacks
- Pegasus spyware email scams
- How to detect Pegasus spyware on your Android or iPhone (iOS)
- How to remove Pegasus spyware from Android and iPhone (iOS)
- Legal and ethical impact of Pegasus spyware
- Scan your device for hidden spyware
While Pegasus spyware was designed by an Israeli cyber-intelligence company to combat criminal and terrorist activities, it has also been used to spy on voices challenging power, like activists, journalists, and whistleblowers.
Data suggests that more than 50,000 people are being, or have been, monitored by Pegasus spyware — with serious implications for their privacy and personal safety. Learn more about this unsettling spyware and get tips on how to detect and remove it in the unlikely event that you’re targeted.
What is Pegasus spyware?
Pegasus is an advanced spyware tool that targets smartphones. Most often used by government actors, it gives attackers real-time access to sensitive data stored on the affected device, allowing them to monitor all sorts of activity. Emails, messages, calls, photos, location, and even camera and microphone data could all be compromised on a phone infected with Pegasus.
Pegasus usually infects mobile devices through zero-click attacks that exploit unpatched vulnerabilities. However, some attacks still lean on traditional methods like phishing which require user interaction, typically in the form of clicking a link that triggers the installation.
Who made Pegasus spyware?
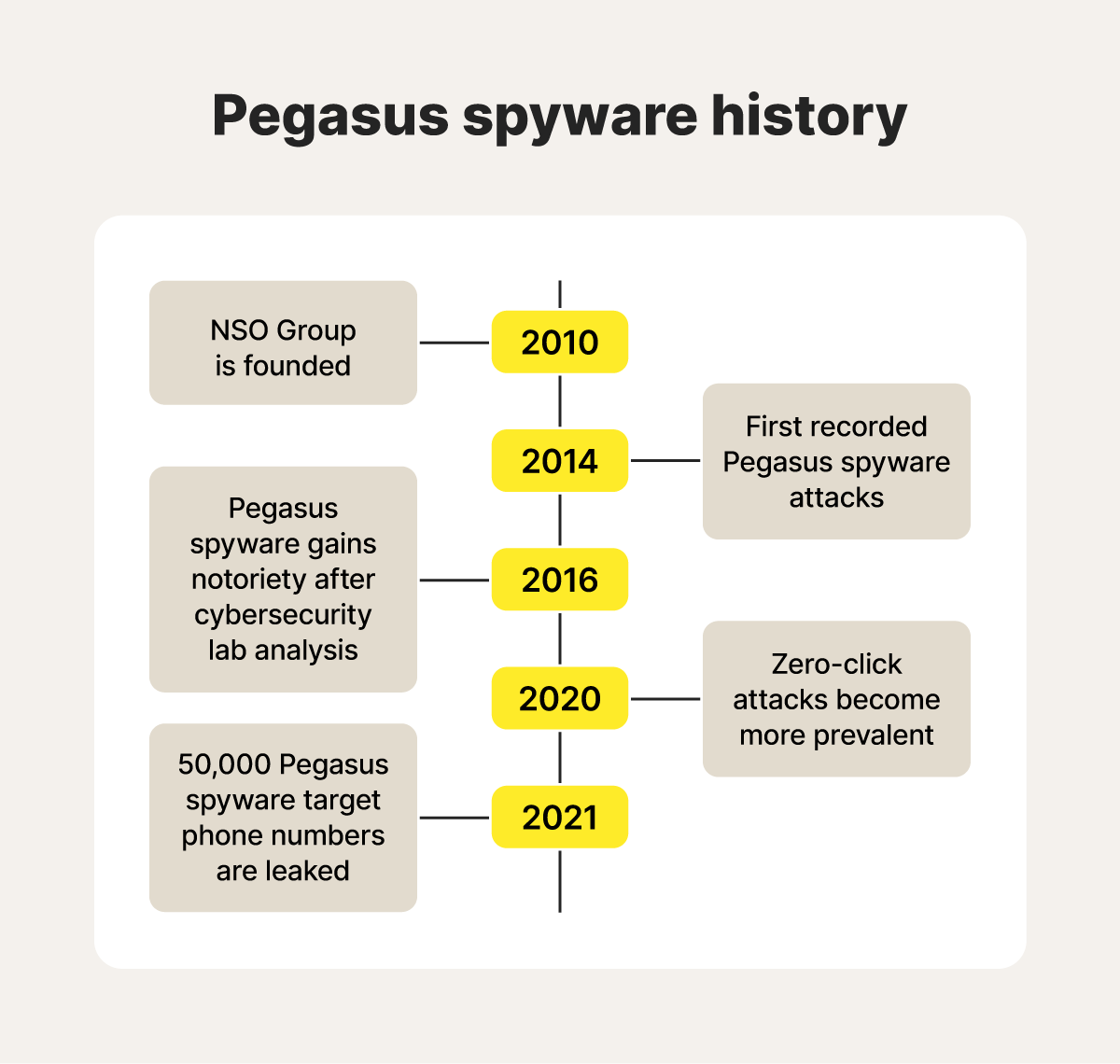
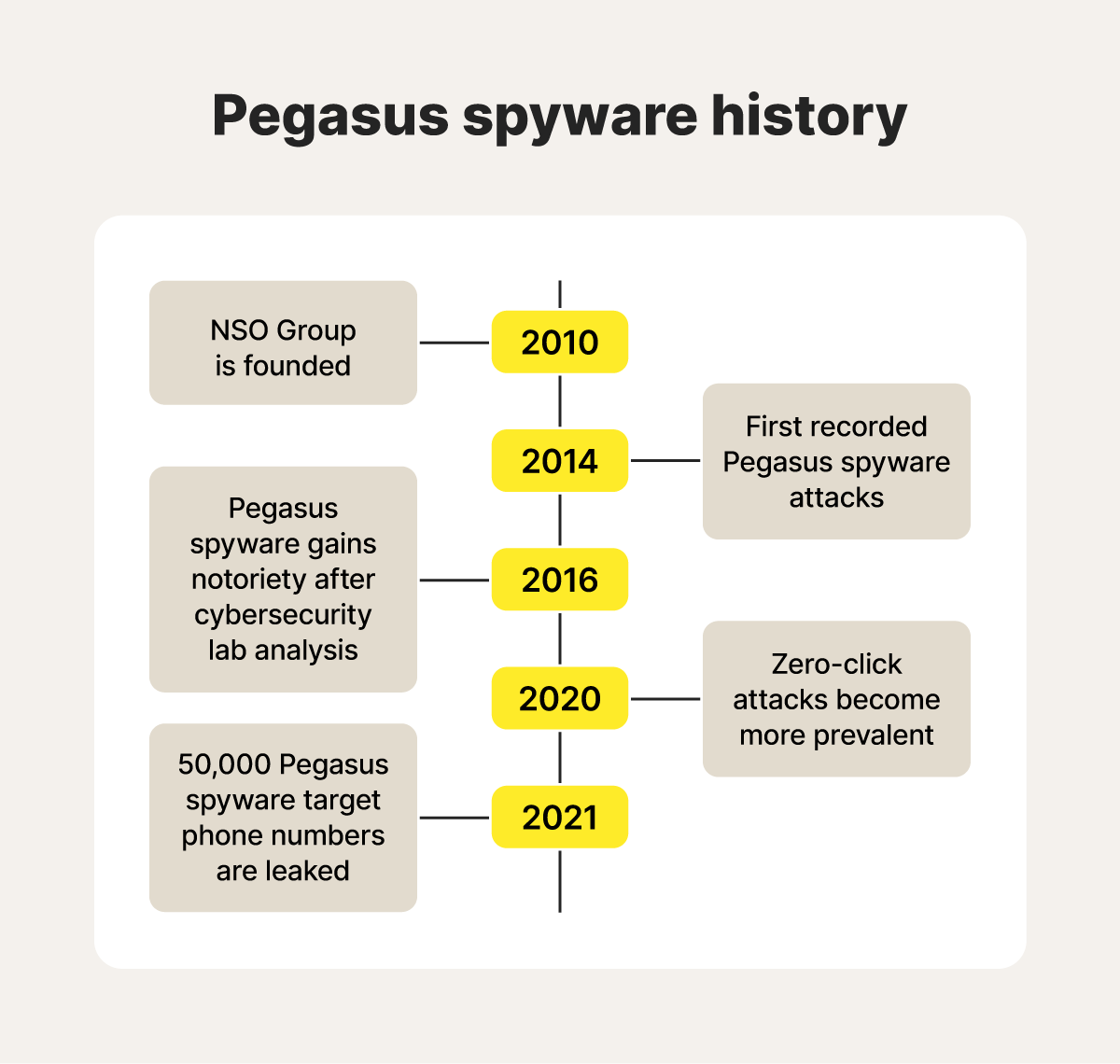
Pegasus spyware was developed by the NSO Group, an Israeli cyber-intelligence firm. The company specialises in creating highly targeted surveillance technology, which it licenses to various government agencies worldwide.
How does Pegasus spyware work?
Once a licence for Pegasus spyware has been obtained, the attacker selects a strategic target, infects their phone using zero-click attacks or a phishing scheme, harvests data, and either watches user activities in real-time or exfiltrates data back to their servers.
Here’s what the process looks like.
Step 1: Infiltration
Pegasus spyware typically infiltrates mobile devices by exploiting unpatched vulnerabilities in the operating system or installed applications, often through methods requiring minimal user interaction.
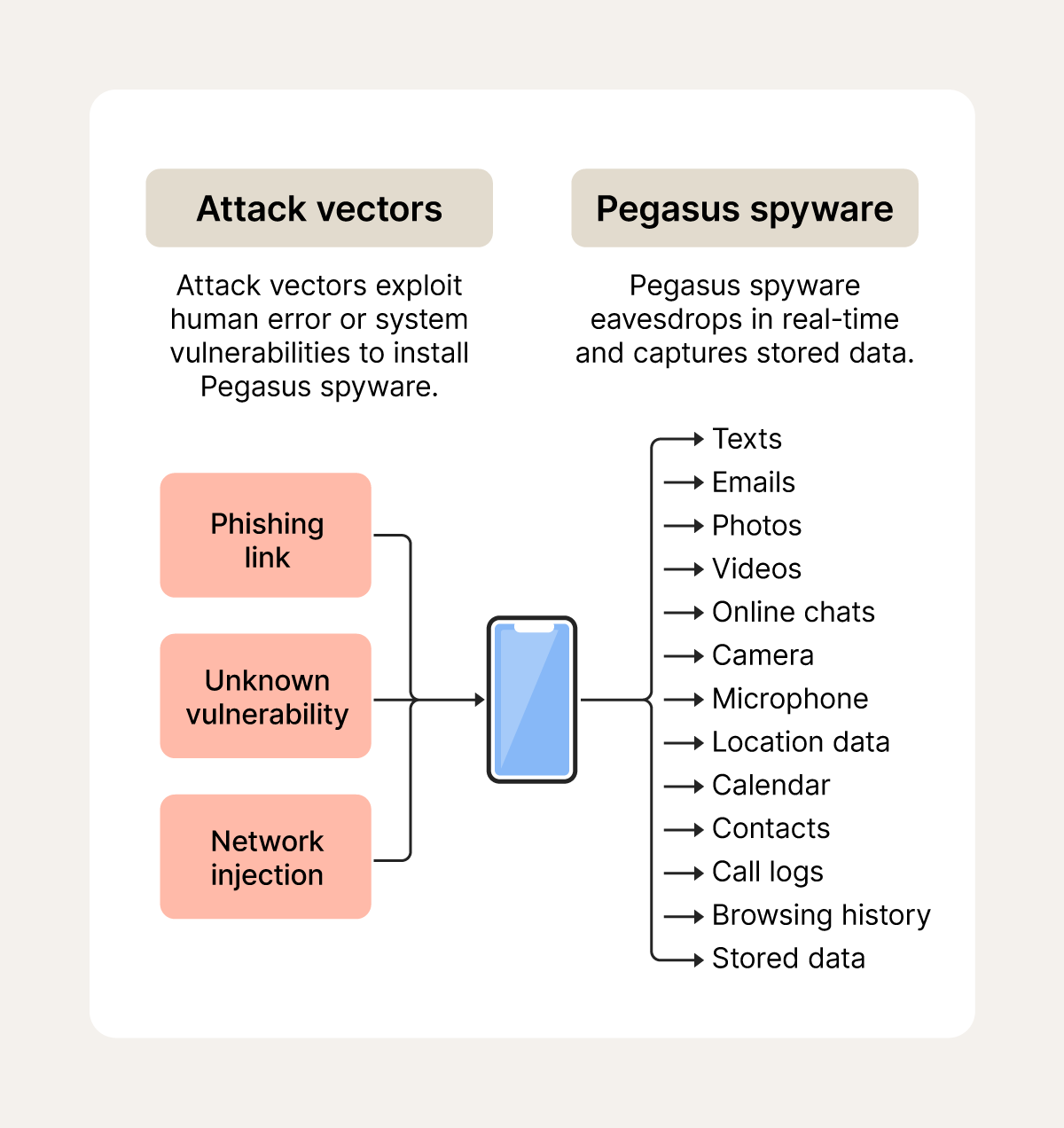
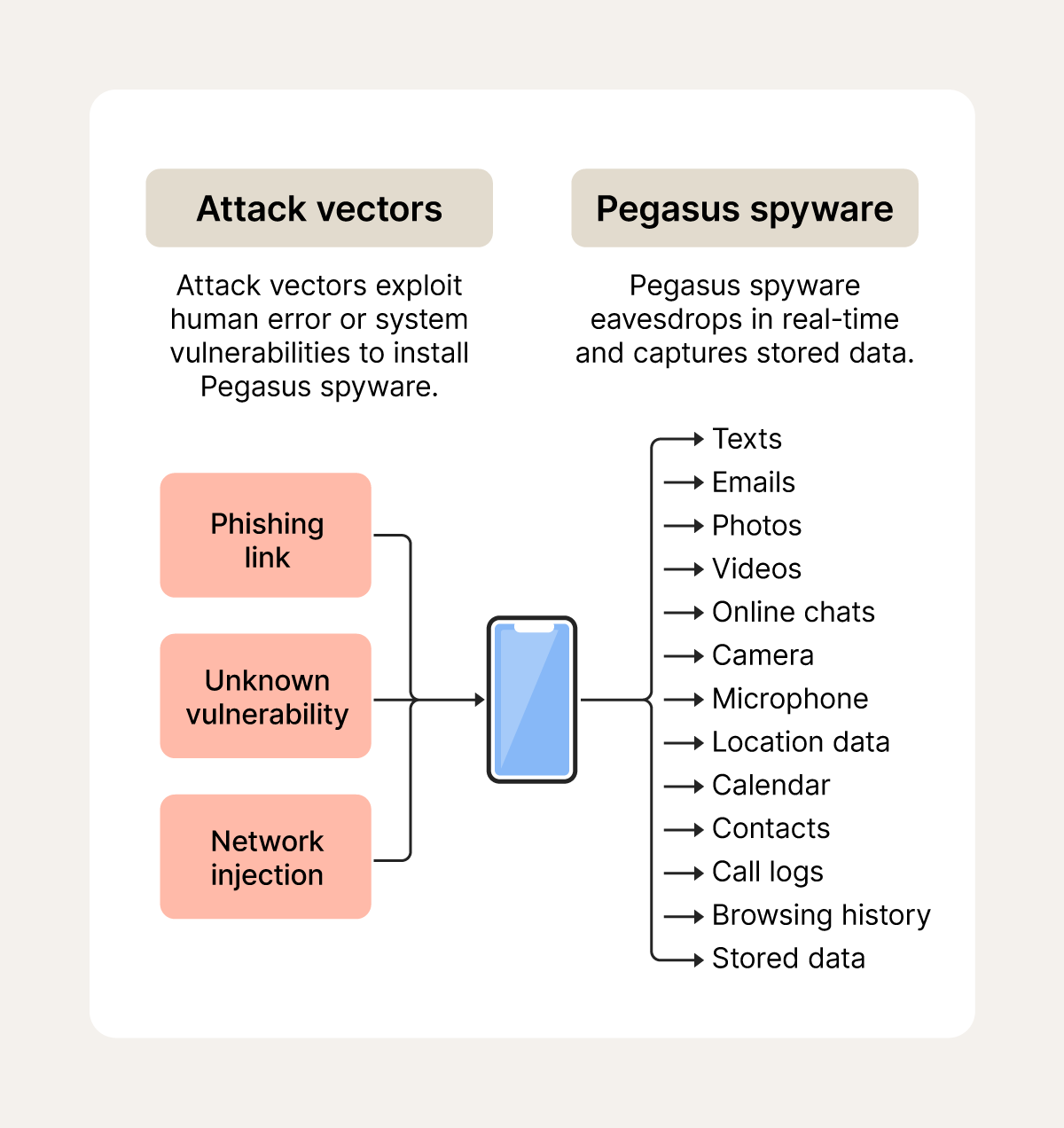
Here are some common attack vectors for this spyware:
- Apps: Pegasus can exploit app vulnerabilities to infect a device without any user interaction in what’s known as a zero-click attack. Attackers could deliver malicious code through compromised messaging apps, for example, allowing the spyware to install itself as soon as a message is received, even if the user never opens it or clicks anything.
- Network injections: When a device connects to the internet, it exchanges data packets with servers. Attackers might intercept this communication and inject specially crafted packets that contain malicious code. If the device’s software has a flaw, it could inadvertently process this code, allowing attackers to install Pegasus spyware.
- Push notification exploits: This attack vector involves manipulating the system that delivers push notifications to a mobile device to execute malicious code or trigger a vulnerability. Pegasus software can potentially exploit this to infiltrate a device through a seemingly harmless push notification without user interaction.
- Phishing: Attackers may impersonate people or organisations to trick targets into clicking on links that trigger an automatic download. Pegasus spyware is more known for sophisticated zero-click exploits, but phishing exploits relying on user interaction still occur.
- Social engineering: Attackers may use social engineering techniques to manipulate targets into performing an action to download Pegasus by pretexting (creating a fabricated scenario) or baiting (offering a desirable download or displaying a news article with a sensational headline).
Step 2: Data harvesting
Once Pegasus infiltrates a device, it can harvest a wide range of data by accessing the phone’s operating system, applications, and memory storage.
Its capabilities mean it may be able to intercept messages from messaging apps like WhatsApp, Telegram, and Signal. It can also access stored data like call logs, contacts, emails, messages, media, browsing history, and location data. It can even reportedly activate a device’s microphone and camera to monitor in-person activity.
Step 3: Data exfiltration
Finally, Pegasus exfiltrates data to attacker-operated command and control servers. Attackers can use the information to track the target’s activities, gain further insights into their personal and professional life, identify their contacts and networks.
Information gathered by Pegasus may even potentially be used for strategic purposes, manipulation, or in support of other military or political objectives.
Known Pegasus spyware attacks
Thousands of people have been targeted in Pegasus attacks. While the spyware was designed as a tool to help law enforcement crack down on terrorism, drug trafficking, and other crimes, in practice, it has also been used on innocent whistleblowers.
Here are just a few examples of Pegasus attacks and the impact the infection had on victims' lives.
Jamal Khashoggi
Jamal Khashoggi, a prominent Saudi journalist and dissident, was brutally murdered in 2018 in Istanbul, allegedly by the Saudi government. Subsequent leaks of forensic investigations revealed the Pegasus program had infiltrated his devices and those of his inner circle, although the NSO group denies this.
Hanan Elatr, a wife of Jamal Khashoggi, was also targeted and believes their private conversations were intercepted — potentially influencing the Saudi authorities’ decision to order his execution.
BIRN Journalists
In February 2025, two Balkan Investigative Reporting Network (BIRN) journalists were targeted in a Pegasus spyware attack. The reporters suspected their smartphones were under attack after receiving suspicious messages on the messaging app Viber.
In this instance, the attackers relied on a relatively clumsy phishing link, a less sophisticated method compared to the notorious ‘zero-click’ exploits. Because of this, the journalists avoided interacting and raised the alarm, protecting their data from prying eyes.
Bahraini dissidents
In 2022, Amnesty International and the Citizen Lab found that a lawyer, a journalist, and a counsellor, all of whom were critical of the Bahraini authorities, were targeted by Pegasus spyware. It’s believed that hundreds of other Bahraini dissidents, whose numbers were leaked online, were also targeted.
This targeted campaign coincided with a crackdown on dissenting online voices and the outlawing of opposition groups, suggesting a calculated effort to monitor anyone who disagreed with or organised against the government.
Pegasus spyware email scams
Recently, there have been numerous reports of people receiving emails claiming that Pegasus spyware was installed on their devices. The emails contain victims’ personal information and a PDF outlining the threat.
They include a sextortion message and ransom demand — often requesting money in cryptocurrencies such as Bitcoin — in exchange for supposedly removing the spyware.
If you receive this Pegasus email, make sure not to interact with it. Don’t reply, contact the sender or click any links. On top of that, you should run a trusted virus and spyware scanner, such as Norton 360 Deluxe, to help detect if your device’s security has been compromised. Then, report it to ScamWatch to warn others.
How to detect Pegasus spyware on your Android or iPhone (iOS)
Typical signs of spyware include a slow device, difficulty logging into secure sites, and disabled security software. However, due to its sophistication, Pegasus is much more difficult to detect than other types of malware and often goes totally unnoticed.
The Mobile Verification Toolkit (MVT), an open-source tool for forensic analysis of mobile devices, can help analyse phones for traces of a Pegasus infection. However, this tool is command-line or terminal-based, so it requires considerable technical know-how. If you’re unfamiliar with forensic analysis and you suspect your phone has a Pegasus infection, consult a cybersecurity expert.
If you believe your phone has been infected with spyware, chances are it’s not Pegasus — unless you’re a high-profile public figure. But that doesn’t mean you shouldn’t take the threat seriously. Norton’s Spyware & Virus Removal Services is on hand to personally help you detect and remove spyware and viruses from your device if you fall victim to a spyware attack.
How to remove Pegasus spyware from Android and iPhone (iOS)
You’ll likely need help from a security service provider to remove Pegasus spyware from Android and iPhone, because specialised tools and knowledge may be needed. However, you can also try to disable the malware on your own by deleting installed files and patching vulnerabilities — here’s how:
- Restart your phone: Restarting your phone can temporarily stop Pegasus spyware if it is relying on short-term memory to complete its processes, but it’s not a long-term solution because the persistent elements on non-iPhone devices can potentially re-establish themselves once the device turns on again.
- Reset your phone to factory settings: Resetting a phone to factory settings can remove Pegasus spyware by erasing all user data, applications, and configurations, effectively reverting the device to a state before somebody installed the spyware. Unfortunately, if you back up your data and restore it after wiping your phone, you risk reinfecting your device.
- Update your apps and operating system: Updating apps and the operating system can help prevent Pegasus spyware from establishing itself on your device in the first place by patching the security vulnerabilities that the spyware uses. However, this won’t help if you already have Pegasus on your phone.
Legal and ethical impact of Pegasus spyware
The NSO Group has come under fire multiple times for its ethically questionable contributions to surveillance, prompting the UN to call for laws to regulate spyware’s use to avoid human rights violations.
The cyber intelligence firm asserts its technology is designed to help government agencies ‘prevent and investigate terrorism and crime to save thousands of lives around the globe’. However, the NSO Group licenses its program to governments known to spy on and punish citizens, hindering privacy and freedom of speech.
The NSO Group’s targeting of app vulnerabilities has also drawn the ire of big tech companies and U.S. lawmakers. In one case, the spyware developer exploited a vulnerability in the popular Meta messaging app, WhatsApp. As a result, the Northern California District Court made a precedent-setting ruling that it’s illegal to exploit these weaknesses to target users, ordering the NSO Group to pay $167 million in damages.
In response to backlash, the NSO Group’s CEO stepped down, and the company has pledged to only sell its software to U.S.-aligned NATO countries going forwards.
Scan your device for hidden spyware
While Pegasus is not a threat to the average person, there are lots of other dangerous types of malware out there, including emerging forms of invasive and sophisticated spyware.
That’s why using strong cybersecurity software is so important to protect your device. Norton 360 Deluxe is a comprehensive security app that can help detect, block, and remove security threats that might be able to spy on you. Plus, it includes a built-in, bank-grade VPN to encrypt your connection and help keep your communications more private.
Editorial note: Our articles provide educational information for you. Our offerings may not cover or protect against every type of crime, fraud, or threat we write about. Our goal is to increase awareness about Cyber Safety. Please review complete Terms during enrollment or setup. Remember that no one can prevent all identity theft or cybercrime, and that LifeLock does not monitor all transactions at all businesses. The Norton and LifeLock brands are part of Gen Digital Inc.








Want more?
Follow us for all the latest news, tips, and updates.